Can Anyone Truly Be Anonymous Online?
Can Anyone Truly Be Anonymous Online?

The Internet is the single greatest information resource available to mankind today. Unfortunately, the Internet of today has become a minefield of data collection and tracking. From advertising companies, to hackers, to governments, the information about where people are going on the Internet is a hot commodity.
Vast numbers of Internet users often assume that no one is viewing their Internet traffic and often use the phrase, “What do I have to hide?” While they may not have any information to hide, they certainly have some that should be protected. In a world where Internet shopping dominates the economy, more and more financial and personal information is being stored on our computers. What steps can be taken to protect this information and is there truly a way to browse the web anonymously? First, we need to look at the methods used to collect all of this information.
As a note, this article is meant to provide a basic overview of online security and privacy. It’s not an all encompassing guide, but armed with these basics you’ll be able to understand the principles and develop a strategy to further protect yourself online.
Cookies
Ask an average person about Internet Security and at some point they’ll likely bring up the subject of cookies. A cookie is a piece of data from a website that’s stored in a web browser when a user browses that site. Cookies can offer useful features like remembering where you were on the page or what was in your shopping cart. Unfortunately, cookies can also provide information about your long term browsing habits, which enable web sites to see where you’ve been and allow them to more effectively target you with advertisements.
Social Media
Almost everyone has at least one social media account and most of us have many more. While these services are great for connecting with friends and family, they’re one of the biggest violators when it comes to privacy invasion. Sites like Facebook and Twitter use cookies to track your web history and use this data to push ads for things they think you’ll be likely to click on.
Sites like Facebook even offer compatibility with commenting systems so you can comment using your Facebook account. The ability to offer services like this comes from using data collection devices like cookies. The problem with these methods is that there’s no public log of exactly what information is being collected. When you browse the web with your social media accounts logged in, you’re potentially allowing those companies access to virtually all of your Internet browsing.
IP Tracking
Every Internet connection requires an IP (Internet Protocol) Address and these addresses are issued by ISPs (Internet Service Providers.) These addresses are unique and can be used to locate a user and where they’re browsing from. An IP Address is an Internet fingerprint of sorts, that leaves a trail of breadcrumbs for anyone following your browsing habits. While many ISPs claim they don’t track individual users IP addresses, there are several instances where IP information was turned over to Law Enforcement or private companies.
One of the biggest examples is IP information being tracked by movie studios to combat movie piracy. A user browsing the web downloads a copy of the latest summer blockbuster and several weeks later receives a letter from a movie studio or their Internet Provider warning them that they’ve violated copyright law. In several cases, users have received warnings from their ISP that a copyright holder has tracked a violation using their IP Address. While copyright infringement is definitely against the law, many people feel that it’s a large violation of their privacy to have their browsing information shared with a private company.
Can You Browse Anonymously?
After seeing some of the methods used to track your Internet browsing, you may be asking yourself “Is there any way to avoid sharing all of this information?” The good news is that using a variety of services and practices, you can severely limit the ability of third parties to track you and your information. The following are just some of the steps you can take to protect your information.
“Private” Browsing
Many people hide behind their browsers “Private Browsing” feature but that doesn’t completely remove you from what you’re doing online. In fact, all that’s needed to give you away is to log into your social network accounts. When you start a new Incognito window in Google Chrome, they make it clear as to what’s actually happening:
Pages you view in incognito tabs won’t stick around in your browser’s history, cookie store, or search history after you’ve closed all of your incognito tabs. Any files you download or bookmarks you create will be kept. Learn more about incognito browsing
Going incognito doesn’t hide your browsing from your employer, your internet service provider, or the websites you visit.
Browser Extensions
Browser extensions are a great first step towards protecting your privacy. Disconnect stops third party tracking and encrypts the data you share with websites. Not only does this increase privacy, it increases your browsing speed since the pages aren’t loading all of the tracking information. Disconnect also advertises that pages can load up to 27% faster than browsing without the extension.
Adblock Plus can be used to hide multiple types of advertising on sites you frequent and can really speed up your browsing experience. By collecting a database of advertising locations on popular sites, Adblock can choose not to display those ads, giving you a faster and cleaner experience. However, since many sites rely on advertising revenue it’s recommended that you whitelist any sites where advertisements are unobtrusive and simple.
Both of these examples are completely free and easy to install in most popular web browsers.
Tor/VPN’s
For the ultimate in privacy protection, you’ll want to use software that is designed to be anonymous. A Virtual Private Network (VPN) offers a user the ability to connect to the Internet publicly from behind a private network. This severely limits the ability of anyone to track information, as all information in a VPN is encrypted and IP addresses can be re-routed through different servers to avoid tracing. While you can configure your own VPN, there are many services that can provide one for a monthly charge. Services like BT Guard allow you to use their VPN connection for $9.95 a month to encrypt all of your browsing including email and web browsing.
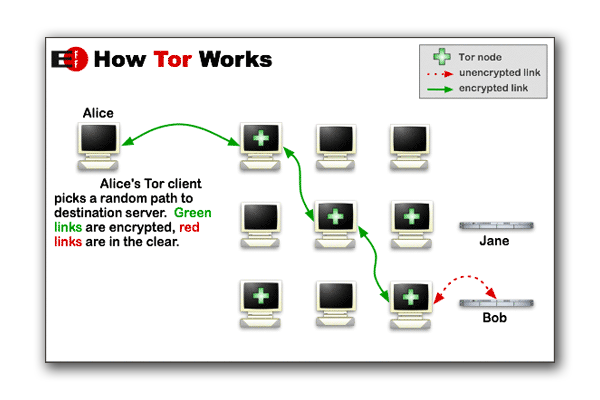
©Electronic Frontier Foundation
Another great privacy option is Tor, a free software that directs your traffic through a volunteer network with over five thousand relays. These relays allow Tor to conceal browsing information from those attempting to track it. Browsing with Tor offers onion routing, a name derived from the many layers of encryption used, much like the layers of an onion. A request is sent from your computer and then routed through multiple relays disguising the origin of the request and IP address information. This makes it almost impossible to track the traffic as no one relay contains all of the browsing information.
A Few Tips
While using these services and methods mentioned above, you’ll still need to keep in mind that there are always failure points in our systems, the largest of which is the end user. The best rule of thumb for browsing the web is if you don’t want the information getting out, don’t post it.
Always be aware of the information you’re giving out and don’t volunteer information unless you know what it’s being used for. With the tips above and a bit more research, users can limit the amount of information they share and improve their ability to truly become anonymous.











Discussion