Password Strategy and KeePass Password Management
Password Strategy and KeePass Password Management
 If you’d like a better perspective on how dependent we are on digital services, imagine your bank account being looted, locked out of your email, and your Facebook page vandalized.
If you’d like a better perspective on how dependent we are on digital services, imagine your bank account being looted, locked out of your email, and your Facebook page vandalized.
While we in the preparedness community like to focus on the beans, bullets, and bullion for someday, information security affects the now.
An AR and a stockpile of Mountain House may give you peace of mind, but until your online services and personal data are secured with strong passwords, you should feel exposed. It is by no means the only aspect of information security to be aware of, but for most regular people, it is the weakest link.
Fortunately, this is one of the threats that is free and extremely easy to neutralize. First I will explain the “why” behind passwords, and then the “how.” By the end, you should have an easier time managing passwords and have a way to secure your sensitive documents.
Theory of Password Strength
So what does password strength actually mean? Simply put, it means minimizing the probability of guessing the password without knowing it. The three factors that play a role in this are character set, length, and entropy.
Character set means the possibilities for each position in the password; a numeric password has 10 possibilities (0-9), a lower-case letter password has 26 possibilities (a-z), and a password consisting of all the ASCII characters has 94 possibilities per spot.
Password length exponentially increases the possible passwords in that space. For example, a single character password would have 94 possibilities (941 options). A two character password has 8836 possibilities (942), and an eight character password would have 6,095,689,385,410,820 possibilities (948). Obviously, longer is better, especially if you are using mixed case characters, symbols and numbers.
Lastly, entropy is one of the most important factors. Entropy is just a fancy word for randomness, or how easy it is to predict the next letter based on the previous. For example, if the first five characters were “11111”, there’s a higher probability of the sixth being “1” rather than “Q”.
This is why password advice is to always have a random password, at least eight characters long, using numbers, letters, and symbols.
How Passwords Are Broken
In a realistic threat assessment, you’re much more likely to have your password stolen as you type it by a piece of malware installed by funny screensaver you downloaded. Also, the number of guesses per second is severely limited on online services that limit the number of guesses and add computer-stopping CAPTCHA’s after a handful of failed attempts.
For now I’ll focus on how passwords are broken in the worst case. This means the attacker has a copy of the password hash or encrypted data on their own machine and the password never changes; for example, a government agency has a copy of your encrypted “photos” and are trying to gain access.
Modern password cracking tools don’t incrementally go through and try each option. They start with pre-compiled lists of English words, phrases, and commonly used passwords. In addition, there are other kinds of intelligent statistical methods that shorten time-to-crack, but assuming you followed the rules above, it will be forced to resort to brute-force guessing.
The next factor in how long it takes to crack is how much parallel computation power can the attacker muster. While modern CPU’s are very fast, it is actually Graphical Processing Units traditionally found in video cards that are the real power-houses of password cracking. The short reason is that regular CPU’s are very good at computing serial calculations (where the input of the next depends on the results from the last calculation) and that GPU’s are good at hundreds of simultaneous, independent calculations. Guessing passwords falls in the latter category.
Using off-the-shelf hardware is so good, US Customs have bought 20 PlayStation 3’s to replace their existing Dell password-cracking cluster. An off-the-shelf Nvidia GeForce GTX 285 gaming graphics card ,which only costs $400, can make an estimated 580 million guesses per second per card. Government and corporate budgets can afford hundreds of these for a cluster.
To estimate your password strength, divide your password’s possibilities (unique characters used to the power of the password’s length) by the best guess of how many passwords can be guessed per second. Our 8-character password would last 12.1 days against 10 GTX 285’s, 6 against 20 cards, etc.
KeePass Password Management
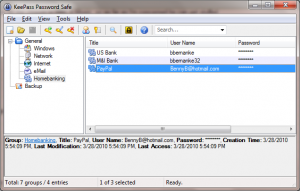 KeePass is an application used to store passwords in an encrypted file, with versions available for Windows, Linux, Mac, iPhone, Blackberry and the Android platform. The format that these applications store the passwords in (.kdb) is a single file containing a database of all your login credentials.
KeePass is an application used to store passwords in an encrypted file, with versions available for Windows, Linux, Mac, iPhone, Blackberry and the Android platform. The format that these applications store the passwords in (.kdb) is a single file containing a database of all your login credentials.
By protecting all of your passwords with a single master password, you get two advantages. The first is that you can u case the in-built password generator to protect all of your accounts with a unique, ridiculous strong password. The way most systems (should) handle passwords are agnostics about length and character set. This means your password can often be a 64-character, full-ASCII set protected password that you never have to remember. If one password is compromised on an online forum, your bank password is still secure.
The second advantage is you’ve reduced the exposure from dozens of systems which all need to be protected to a single point of failure. Now you can focus on remembering an extremely strong password and securing that single file. Your KeePass database can be protected by an unlimited length password, and so I recommend Robert Hensing’s advice which is to use a pass-phrase.
Use an entire sentence which contains punctuation and numbers, but is memorable to you; avoid well known phrases or song lyrics (as those would likely be checked by password guessers), but something unique like “My first dog, Fluffy, died when he was 12 years old.” This is a 52 character password with mixed case letters, numbers, and symbols; while it does not have perfect entropy, it’d be damn hard to crack by anyone but the most determined and knowledgeable attacker.
By having it password protected, you could reasonably email the database to yourself or copy it to a thumb-drive and keep it at another location to keep it secured. It technically exposes you to a higher risk of getting cracked, but hard-drives die, computers are stolen, and houses burn down. I’d rather take the chance the Black Helicopters decrypt my SSL message to GMail than not back it up and lose access to all my systems.
Besides, a real-world attacker can always use rubber-hose cryptanalysis.
Attaching and Encrypting Files
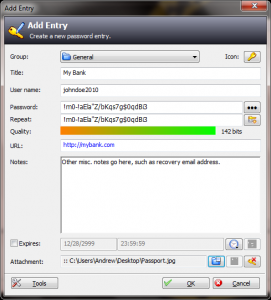 The other major (and underrated) feature in KeePass is the ability to include other files “attached” inside your database. On an entry, you can attach any type of file, including ZIP, to an entry that will keep it encrypted an inside of the KDB file.
The other major (and underrated) feature in KeePass is the ability to include other files “attached” inside your database. On an entry, you can attach any type of file, including ZIP, to an entry that will keep it encrypted an inside of the KDB file.
Without having to install or deal with more complicated file encryption schemes, this is a dead-simple to way to keep a limited number of files fairly secure.
Final Notes
Attackers come in all forms, and whether you’re keeping your secret plans safe from the New World Order, or just keeping your savings account safe from thieves, the principals of good information security remain the same. Passwords are not the sexiest of topics, but they are the keys to your online life.
Taking a few minutes to put your logins in order will, at worst, keep you from having to recover your password, and at best, save you from a serious financial or privacy blow.
Editor’s Note: Andrew Stuckey has degree in Information Systems from the Wisconsin School of Business and is developing CitizenArmory.com, an online marketplace for firearms transactions. Please join us in welcoming him as a guest writer on ITS Tactical.










Discussion