PSD Concepts: Attack Recognition and the Art of the Ambush
PSD Concepts: Attack Recognition and the Art of the Ambush
- PSD Concepts: Introduction and Daily Routes
- PSD Concepts: How to Detect Surveillance and Counter
- PSD Concepts: Attack Recognition and the Art of the Ambush
- PSD Concepts: Why You Should Conduct Vehicle Searches
Now that you have your routes planned out and have a basic knowledge of surveillance detection its time to talk about attack recognition and the ambush.
We are going to continue to focus on your route from home to work and attacks to your vehicle. I want to focus on your vehicle and travels and not worry about avoiding a sucker punch on the street.
Attack recognition is a whole other animal when you talk about self defense (Tony Blauer has excellent information on physical attack recognition and response).
What’s an Ambush?
An ambush is a surprise attack, from a concealed position. It’s used on a moving or temporarily halted enemy to destroy or capture him and his equipment. This definition is taken right from Infantry 101.
Ambushes have been around since the beginning of ancient warfare and are still in use today in modern combat. So long as there’s war, there will be the art of the ambush.
Attack Recognition
When you can recognize an attack you can use your pre-planned tactics to escape the assault. Your attackers have several advantages; they select the target (you), the time, place and the nature of the attack. Your planning, analysis and vigilance can help take away this advantage.
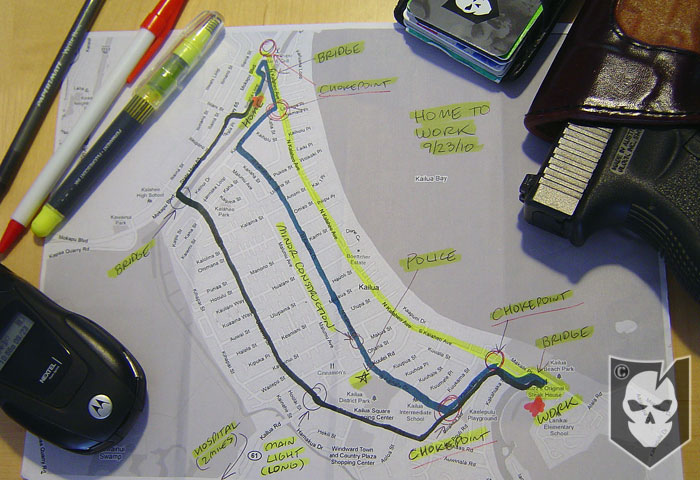
Since you have a good route survey and have identified potential attack sites you should have developed a response if attacked. You also have a good understanding of when and where each attack might occur which allows you to be at peak alertness at critical points along your route.
The Good News
Within each critical point, your attackers also have certain disadvantages. These are often recognizable and evidence of an impending attack.
- Prior to the attack someone must observe your approach and signal the attack team. Most likely this will be from a fixed location just outside or just inside the kill zone.
- You may also detect the communications between the surveillance (target identification) and the disguised attack team. They may initially appear unrelated but if you are being surveilled or set up for an attack they’ll have to communicate. If the communication appears urgent or just blatant then an attack my be imminent.
- In the age of cell phones, blue-tooth, computers and electronic communications you may think you can’t tell who is talking to who. Think about your drive today; you see people talking “to themselves” all the time in their cars and on the sidewalk. But human nature is human nature and people who are involved with a stressful event such as being involved in an ambush will tend to show it in some way. If you are/were in the military or law enforcement you know how you get right before an ambush or take down. Look at your buddies on the next operation and see how their body language and demeanor changes right before “go”.
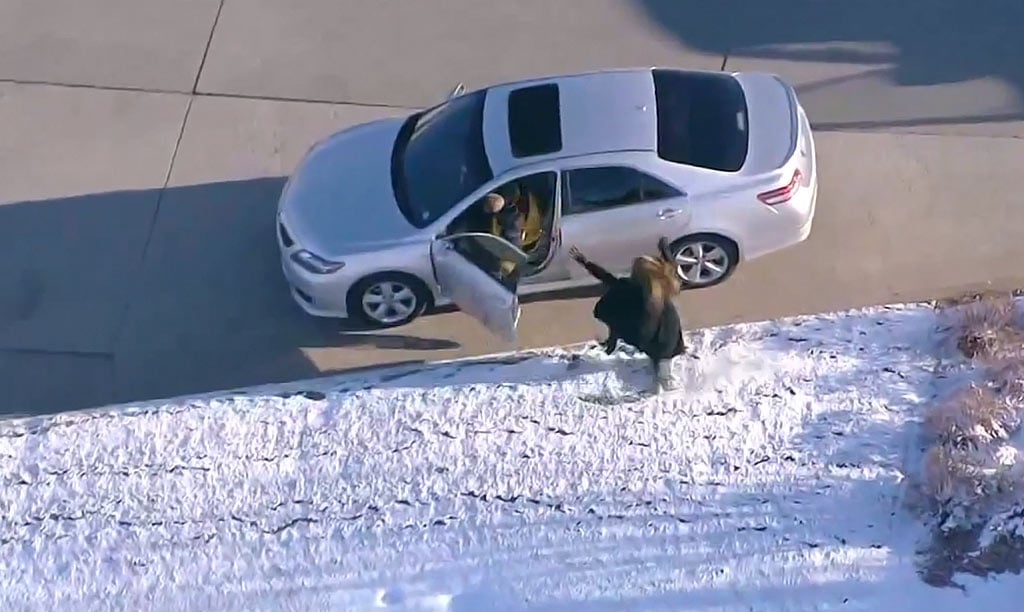
- The attack is most commonly initiated by a ruse or disguise. You see this in the movies all the time (the movie HEAT has a great ambush scene of a armored truck). The garbage truck pulls into the roadway blocking your path, the attractive woman with the broken down car, or a staged crash. These type of ruses are used to slow you down in the kill zone and allow them to start the assault. This is very popular with the Mexican drug cartels. They are very good at using large trucks and buses to block and trap their targets in the kill zone.
- If a vehicle pulling out is legit it will continue on its way and the people around it will also continue with whatever they were doing. If it is a ruse the car will stop completely and the people who were previously disassociated with it will start directing their attention toward you.
- The attack has to transition from the disguise to the action (attack). People will have to break from their concealment or cover. If this happens on one of your pre-planned attack sites this should offer the opportunity to escape.
- You must be totally dialed in when entering each chokepoint. If you recognize any pre-incident indicators hold well back of the problem. If it’s nothing it will quickly dissolve. If not, then you hopefully haven’t entered the kill zone (or the “X”). Separate yourself with time and distance to disrupt the attack plan using evasive tactics (J-turns, Bootlegs, etc).
Certain chokepoints like blind corners, sharp hills, or bridges may prevent you from seeing a upcoming attack. Since we’re talking individual tactics, you wont have that advance team clearing your route for you. This means you may drive right into a potential attack site. Stand-off attacks or IEDs/VBIEDs may not offer you any opportunity to recognize the impending attack.
Here in the states the likelihood of someone shooting an RPG at your vehicle from a rooftop is pretty remote. This goes back to your route survey and analysis; think about your potential threat and try to plan accordingly. You shouldn’t plan for driving into a pack of zombies (no matter how fun that would be).
Remember, attack recognition is only a single part of your personal security posture. Our next article will be about searching your vehicle for the three Bs’: bombs, bananas, and bad things. If you have never had any training on searching a vehicle I hope this will be a eye opening (and fun); another tactic to add to your toolbox.









Discussion