Securing your Digital Life: Home Wireless Network
- Securing your Digital Life: Home Wireless Network
- Securing Your Digital Life: Simple Tips for Your Devices in Public
In today’s world, we rely on electronic devices more than ever before. These devices allow us to connect and share information throughout the world at a speed that was never thought possible. We can now share our ideas instantly through laptops, smartphones, tablets and other devices.
In a world where information moves at the speed of light, the need for security has never been higher. Our devices and identities are subject to a variety of attacks both physical and electronic. There are many methods and practices for securing your information. Today, we’ll start with the basics.
Having a network in your home is a great way to share information between your devices without physically transferring it. The most common way people network their devices in the home is through the use of a wireless router. Wireless routers are great because they allow us to access the Internet anywhere in the house. However, if not secured properly, routers can be a great point of attack for someone looking for your information.
Most good quality home networking equipment provides certain settings that can help to secure the wireless network. In this article we won’t cover any specific hardware, but we will discuss common settings and best practices. Remember, network security is no different than security in other areas. We advocate a multi-layered approach that doesn’t rely on just one point of failure.
Equipment and Services Needed
- A connection to the Internet (usually broadband)
- A wireless router
- Ethernet Cable
Secure the Hardware
Once you have your Internet connection up and your wireless access point working, you will need to alter many default settings to begin to secure the network. Default login credentials are easily available online for much of the common hardware out there, which gives an attacker easy access to your new router. Your first priority is changing the administrative user name and password on the wireless access point.
You’ll also want to consider the physical security of your access point. By installing the access point in an insecure part of the house, such as a garage, you allow an attacker the ability to physically reset your access point and gain entry by using the default credentials. Once an attacker has physical access to any piece of computer equipment, the game is over.
Let’s pause for a moment and talk about passwords and user names. With the abundance of online services, it is becoming quite difficult to keep track of all our user names and passwords. Especially with something that you log in to as infrequently as your wireless access point. You can’t let your guard down with such a critical point of attack, so choose a password that is at least 8 characters in length and mix in numbers, upper case letters, and punctuation. For more information, see our previous article on password strategy.
Secure the Signal

Now that we have secured our access point, let’s secure the wireless signal. Most access points will give you several options for wireless encryption. You’ll want to choose the most secure settings your access point will allow. Often, the most secure encryption method is WPA2. Make sure that you choose a strong encryption key.
One method to secure your signal is to choose not to broadcast the name, or SSID, of your network. This will stop some casual hotspot snoopers and in a layered security model, it’s a great practice.

All network devices have a unique identifier called a MAC address. You can control access to your wireless network by telling the access point to only allow connections from certain MAC addresses. Follow the instructions in the user manual of your access point to enable this filtering. A MAC address is easily spoofed by an attacker, but once again, this is a good practice in a layered security model.
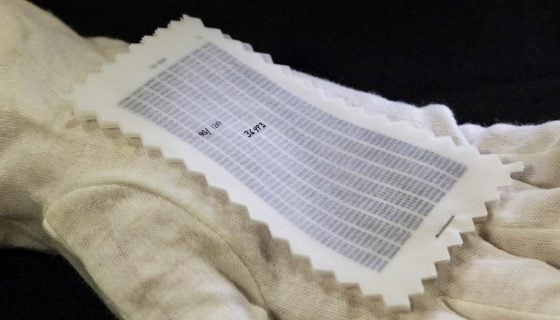
Computers will have MAC addresses on their wireless cards and all Wi-Fi devices have them, you just may have to do some searching to find yours. These photos show an example of one laptop’s MAC address location.
Other Security Measures
Most routers will have a remote login, which you will need to disable to ensure that only a local connection can log in. Consider enabling the family controls that turn off your network at certain times of the day. For example if you are at work during certain periods or you never use your network from 2 a.m. to 6 a.m., why does it need to be on? Make certain your devices don’t auto connect to open Wi-Fi networks. If the network is not yours, it is not secure. That doesn’t mean you shouldn’t use unsecured networks, you just need to be more cautious about what you are doing on those networks. Don’t just set it and forget it. Review your security settings once in a while. If there has been a change to your settings that you didn’t make this can signal that there has been a breach in your security.
Most Common Attack Vectors
The most common attack to home networks is not a malicious user sitting in an unmarked van on the street stealing your credit card info as you type it in to purchase something online. It’s viruses, worms, spyware, and malicious programs that steal your personal information Using the methods we’ve mentioned above, as well as having a good antivirus program (or using an alternative operating system less susceptible to common viruses) and good browsing methods can prevent these attacks. Good browsing methods include checking a website’s URL and encryption methods before entering any personal information. Internet browsers will verify a website’s credentials and many will display the information in the address bar of the browser. If you see anything out of place or are suspicious of any website you visit, do not enter any personal information.
Detecting an Attack
Intrusion detection is tricky and, by definition, can only be determined after an attack has taken place. If an individual has attacked your network, contact law enforcement and report it. Identity theft is a serious crime and carries severe penalties. (There were 10 million victims of identity theft in 2008 in the United States alone and, on average, victims lose between $851 and $1,378 out-of-pocket trying to resolve identity theft.) Monitor your systems and notice changes that you did not make. Always have updated antivirus programs, firewalls, and monitoring software installed. With these multi-layered methods we have mentioned, you can expect a reasonable level of security in your home network.










Discussion