Bugging Out with Personal Information
Bugging Out with Personal Information
A copy of your personal information should always be included as part of a bug-out bag or evacuation kit. I have often been asked why we need this information and have had people say that they have this information secured in a safe in their home.
Is that information actually safe? Are you certain that your safe will survive a major fire? What if a tornado destroys or removes you house and it just can’t be found? A nuclear emergency, such as the one in Japan, might mandate an evacuation where you are not allowed to return.
There are many reason to carry important personal information when you evacuate. I like to carry a backup of my personal information on me at all times, as well as in my bug-out bag. The real problem is securing that information. I have seen it often recommended that all your personal information be placed in a file folder and kept in a large zip-lock bag. Obviously, if this file is found or stolen, you have a real potential identity theft problem. So what do you do?
The IronKey
 I used to carry my personal information on a USB flash drive. Unfortunately, for years, I could only find software encryption, which is not always as secure as it is made out to be. Some software encryption can be easily broken, leaving your information vulnerable.
I used to carry my personal information on a USB flash drive. Unfortunately, for years, I could only find software encryption, which is not always as secure as it is made out to be. Some software encryption can be easily broken, leaving your information vulnerable.
I was limited to this solution until I met a reader of my book, Build the Perfect Survival Kit, who worked for a large bank. For work, he used a product that was designed to meet the most demanding military, government, and enterprise security requirements. Needless to say, I was very interested. It was just what I was looking for!
The device is the IronKey, an extremely secure USB flash drive, ready to protect data everywhere it goes. There are various models of the IronKey, but the basic model, the S200, is more than adequate for the purpose of carrying confidential information. They are available in 2 GB, 8 GB, and 16 GB. The other models provide features more for business applications, which are unnecessary for my needs.
So what is so great about this USB flash drive? The IronKey is the only USB flash drives validated to meet the stringent Level 3 requirements of FIPS 140-2, a U.S. government computer security standard. The S200 protects data with strong AES 256-bit hardware encryption. It has “always-on” data encryption, whereby all user data is encrypted with AES CBC-mode hardware encryption. Unlike software-based encryption, this “always-on” protection cannot be disabled. Since the IronKey Cryptochip generates and stores strong, random encryption keys, encryption routines run faster and more securely than on any software-based encryption system.
Practical Applications
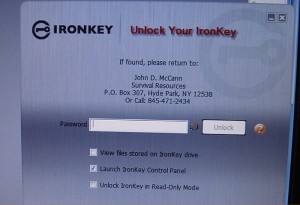 This all sounds good, although a little technical, but it was some of the other security features that sold me. This device is really physically hardened. Its rugged metal casing protects it against physical damage, and the internal components are sealed to protect against tampering. It far exceeds military waterproof requirements. No one can access files stored on an IronKey drive unless they authenticate with the correct password. All encryption and password verification are performed in the hardware, and cannot be disabled by malware or a careless user. Self-defending IronKey drives also provide hardware-level active protections against the spread of malicious code.
This all sounds good, although a little technical, but it was some of the other security features that sold me. This device is really physically hardened. Its rugged metal casing protects it against physical damage, and the internal components are sealed to protect against tampering. It far exceeds military waterproof requirements. No one can access files stored on an IronKey drive unless they authenticate with the correct password. All encryption and password verification are performed in the hardware, and cannot be disabled by malware or a careless user. Self-defending IronKey drives also provide hardware-level active protections against the spread of malicious code.
When an IronKey drive is plugged into a laptop or desktop computer, the user must authenticate with a password before encryption keys are enabled and data and applications are accessible. Unlike software-based encryption, the IronKey protects against cold-boot and malware attacks by not exporting AES encryption keys to the host PC. IronKey Basic protects against brute force password guessing attacks by using non-volatile access-failure counters stored on the Cryptochip itself. If a thief tries to break into an IronKey drive and enters 10 incorrect passwords, the Cryptochip securely erases all encrypted data with patent-pending Flash Trash technology. This ensures no data can be recovered from the device. If the IronKey detects a physical attack, it will initiate a self-destruct sequence (kind of reminds me of Mission Impossible). It is nice to know that if you lose this device, the information on it will not get into the wrong hands!
There is a lot more information I could provide in regard to the IronKey USB flash drive, but I think you get the idea that this is a great way to securely carry personal and confidential information. Both my wife and I carry one on our key ring, and have an extra for the bug-out bag.
Personal Information
What type of information should be kept on such a device? Although not a complete list, the following is information that might come in handy:
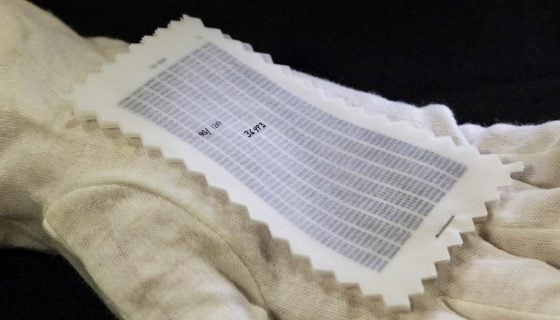
- A file containing actual scans of important identification and documents, such as: drivers license, passport, social security card, pistol permits, birth certificate, marriage and death certificates, the deed to property owned, vehicle titles, contracts, insurance policies, wills, and medical prescriptions.
- A file containing emergency phone numbers: personal contacts, doctors, dentist, healthcare provider, insurance companies, and central station security provider.
- A file with credit card information: card numbers, expiration dates, security codes; and information to contact the provider, should a card be lost or stolen.
- A photo or video inventory of valuables in your home, to include: computers, firearms, pantries and other areas where emergency supplies are maintained (you might have to prove to an insurance company that such items existed). I also like to show the actual house from various sides, outside, as well as the contents of each room, inside. Don’t forget garages, out-buildings, tools, etc.
Obviously, there is other information that can be contained on such a secure device. By carrying a copy of your personal information on a secure device, you will always have a backup, even if you lose your home or wallet. As always, be prepared to survive, and always have a backup!
Editor-in-Chief’s Note: Please join us in welcoming John D. McCann as a contributor on ITS Tactical! I’ve been a longtime reader of John’s work and his first book, Build the Perfect Survival Kit helped me design the kit I EDC. John is also the owner of Survival Resources, a company that specializes in survival kits, survival kit components, and outdoor skills courses. He’s just released a new book too that I’m currently reading, called Stay Alive! Survival Skills You Need.










Discussion