Data Leaks: Location Based Services and Why You Should be Concerned
Data Leaks: Location Based Services and Why You Should be Concerned
- Data Leaks: How My Car Betrays Me
- Data Leaks: A Frappuccino and Your Customer’s Bank Accounts To Go
- Data Leaks: What you Should Know about Rootkits
- Data Leaks: Location Based Services and Why You Should be Concerned
This week we wrap up the Data Leaks series, explaining the ideas, and risks, of location- based services (LBS).
Imagine someday in the future walking into the food court at the mall and being pummeled with text messages from every vendor, each trying to entice you over to their counter, offering coupons and deals tailored to you.
How did they know when to text you? Your cell phone service provider told them you were in the area, and the clock told them it was the lunchtime hour.
Mobile LBS
This is a realistic look view into the types of services that cell phone companies, the owners of your cellular related data, are banking on to drive up their revenue in the years ahead. Earlier this year Juniper Research reported that revenue generated from mobile location-based services could top more than $12.7 billion within 5 years. The report alluded to the fact that Asia and Europe continue to lead the US in mobile technology adoption, so perhaps those of us in the states won’t feel LBS as strongly as our overseas friends, but LBS is coming to a mall, stadium, and even a ski resort near you.
Perhaps surprisingly, the US already has federal laws on the books that are protecting you from a barrage of vendor text messages. The Can Spam Act of 2005 made it illegal to send messages to your phone without you explicitly opting in first. Unfortunately, so many of us are willing to pull out our phone to vote for the American Idol, Dancing with the Stars, real-time football polls posted during the game, etc. that we are, in effect, opting in to some degree if we were to take the time and read the small print on the bottom of the screen.
Two weeks ago ITS provided guidance for disabling Facebook Places, a service demonstrating that the social networking establishment has already begun to shift their focus to working with your location. The key driver behind LBS is the fusion of the venerable GPS and ubiquitous network access offered by today’s smart phones. The assumption being made here by these sites is that just sharing what’s on your mind isn’t enough, and let’s face it–teens want to know where their social circle is.
Tracking Skiers
 Social networking sites and cellular providers aren’t the only ones looking to capitalize on LBS. Just last week Vail Resorts unveiled an ambitious plan called Epic Mix, a combination of Web and mobile apps that each log the skier’s activity. Keystone is slated as the first resort to roll out the service in early November. How does the resort plan on tracking you? The resort is expanding their use of RF-enabled lift tickets to serve up data to the applications.
Social networking sites and cellular providers aren’t the only ones looking to capitalize on LBS. Just last week Vail Resorts unveiled an ambitious plan called Epic Mix, a combination of Web and mobile apps that each log the skier’s activity. Keystone is slated as the first resort to roll out the service in early November. How does the resort plan on tracking you? The resort is expanding their use of RF-enabled lift tickets to serve up data to the applications.
The initial service offerings are mediocre; the readers are only located on ski lift entrances. The CEO of Vail Resorts, Rob Katz, was quick to point out that the service may be improved in the coming years to track precise skier location on the mountain, and they intend to give skiers the ability to easily opt-out.
Likewise, the company has for the time being ruled out partnerships with outside online services. If LBS gains momentum, one would expect the company to revisit this decision in the name of the almighty dollar.
Foursquare
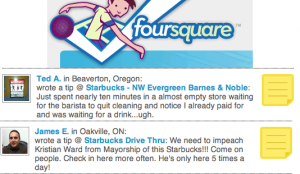 Companies like Foursquare have created novel online games, encouraging people to leak their location in an effort to gain virtual social popularity by becoming the mayor of the local Starbucks, for example. Other companies like aka-aki and loopt are creating services that attempt to expand your social circle by surveying the people around you in everyday life.
Companies like Foursquare have created novel online games, encouraging people to leak their location in an effort to gain virtual social popularity by becoming the mayor of the local Starbucks, for example. Other companies like aka-aki and loopt are creating services that attempt to expand your social circle by surveying the people around you in everyday life.
With the release of new, more powerful operating system’s like the iOS 4 from Apple that can run applications in the background on your phone, your location is always being transmitted.
But aren’t all of these aimed at teens? On the contrary, published statistics indicate that these sites are aimed at young, educated adults, where 70% have a 4-year degree. How popular are they? Foursquare is reported to have over 2 million users, and loopt over 4 million. And the marketers are all salivating, looking to target each of them with mobile coupons and personalized advertisements.
What’s the Problem?
This is all great- but how does any of this relate to a Data Leak? It’s actually a 3-tiered problem. On the primary tier we have the manufacturers and app store managers like Apple and Samsung. Apple’s privacy-friendly edict that it would block apps whose sole purpose is to use location-based information to deliver ads shocked the CTIA Wireless 2010 tradeshow in March. At the same show, Samsung indicated its belief that reasonable limits need to exist. Keeping an eye on the apps you download to your phone and the handset you choose to purchase will be more important. The iPhone, for example, prompts the user to allow a non-Apple app access to your current location, and the phone also displays an icon in the status bar whenever the GPS is being used by an application. Pay attention to these features, and always keep in mind that your phone is automatically geo-tagging your photos and others can easily access this data when they download the photo. Of course, this assumes your phone hasn’t had a rootkit installed!
On the second tier lie the cellular providers, like Sprint, who actually own the data. Wired.com reports that Sprint provided GPS data to the Feds over 8 million times over a 1-year period spanning 2008 to 2009. Sprint, in its defense, claims that the 8 million times misrepresents just how many people were tracked. The linked article elaborates further. The report re-enforces the simple fact that Sprint, and all the other cellular carriers out there, are keeping track of your cell phone’s movements. What they choose to do with that data, how long they keep it, and under what conditions they choose to share that data should concern each of us.
Finally, on the third tier lie the app providers and the marketing companies that want to drop in their ads in the middle of your user experience. Their business plans are predicated upon having access to your location, either directly from data feeds or via an explicit opt-in request from the user. Suffice to say, opting-in on these apps is equivalent to opting-out of your right to location privacy.
Presently, the worst offenders are the cellular providers. A presentation at DefCon 18 from members of the WiMAX hacking group (wimax2010.ppt) documented the fact that Opt-IN is the DEFAULT for everyone using WiMAX. This includes all of Sprint’s 4G customers, and anyone utilizing Clear, Comcast, Time Warner, etc. for mobile internet services. Sadly, the only way to opt-out is to push and push until you finally reach the engineering department, as there is neither a web page portal with a switch for the consumer to opt-out nor plans to develop such a page according to the WiMAX hacking group.
2010 Data Leaks
The concludes this year’s Data Leaks series, based largely on eye opening presentations from BlackHat 2010 and DefCon 18. Educating yourself about the data leaks in your life is important if you value your privacy. Manufacturers, ISPs, marketing companies, etc. are all looking out for their stockholders, not you the consumer. Knowing what data your leaking, and where, gives you the ability to make more informed decisions. Only time will tell what the hackers have up their sleeves in a year from now!












Discussion