Data Leaks: A Frappuccino and Your Customer’s Bank Accounts To Go
Data Leaks: A Frappuccino and Your Customer’s Bank Accounts To Go
- Data Leaks: How My Car Betrays Me
- Data Leaks: A Frappuccino and Your Customer’s Bank Accounts To Go
- Data Leaks: What you Should Know about Rootkits
- Data Leaks: Location Based Services and Why You Should be Concerned
Last week we kicked off a four-part series on Data Leaks with a lead article about vehicular data leaks. In today’s article, we’ll be diving into the realm of free WiFi.
This series is designed to look at how ordinary things we take for granted encroach on our perception of privacy. This series isn’t about ridiculously risky, yet highly popular, opt-in social networks–like blippy, a web site that divulges recent shopping details via sharing credit-card bills among friends.
If any member of this site participates in blippy.com, stay put–the black rendition van is on its way to your location at this very moment to knock some sense into you.
Instead, the Data Leaks series focuses on unexpected data leaks; ways you might be leaking the personally identifiable information that data thieves profit from. This week’s article leaves the car in the garage and focuses on the coffee joint around the corner where you login to pay your bills each month.
Free WiFi
 Free WiFi Hotspots are all the rage these days. Access to free WiFi isn’t yet ubiquitous, but it is visibly on the horizon. From McDonald’s to Starbucks, airports and barbershops, companies have realized that giving their waiting customers something to do for free provides a better customer experience. Odds are if you’re reading this article, you’ve likely plopped open your laptop at some point in time and connected to a WiFi access point at one of these places.
Free WiFi Hotspots are all the rage these days. Access to free WiFi isn’t yet ubiquitous, but it is visibly on the horizon. From McDonald’s to Starbucks, airports and barbershops, companies have realized that giving their waiting customers something to do for free provides a better customer experience. Odds are if you’re reading this article, you’ve likely plopped open your laptop at some point in time and connected to a WiFi access point at one of these places.
It is imperative to understand that the focus here is on WiFi and that the data leaks discussed here affect all of the widely popular 802.11 variants: a, b, g, and n. In no way are these leaks the responsibility of the aforementioned illustrative vendors who are innocently working to create a better customer experience. The fault lies directly with the technology vendors who still can’t seem to wrap their arms around the fact that security matters. (I’ll avoid getting on a soapbox here and leave it at that…)
During the National Defense Industrial Association (NDIA) conference held last week at Naval Surface Warfare Center-Crane, VADM McRaven issued a challenge to the industry: give me WiFi solutions that meet or exceed CNSS Policy No. 15 Fact Sheet No. 1. There is a reason why military commanders aren’t walking around with iPads on their base sharing classified systems: All present WiFi security schemes are effectively broken to some degree and susceptible to attack.
Access Point Security
Every WiFi access point (AP) is effectively limited to a few choices for creating a secure connection between the AP and the client, e.g. a laptop. Most customer-driven commercial entities like McDonald’s are installing APs that are expressly open with no security. Home users will either leave their access point open, or use WEP, WPA, or the WPA2-Personal variant. Enterprise installations are typically going to implement the WPA2-Enterprise variant. An additional form of protection is filtering client connections based on the “unique” serial number assigned by the network card manufacturer, known as the media access control (MAC) address.
On the surface there appears to be a plethora of security choices, yet with a minimal amount of research it becomes clear why the military doesn’t to date trust any 802.11 variant for transmission of classified material. To better understand why, let’s look at each of the security variants and why they are at best an inconvenience to a determined hacker looking for personally identifiable information. Before we do that though, a few facts and terms must be considered and introduced.
Consider this fact: the frequency bands used by WiFi APs all travel through walls to some degree. Also, an overwhelming majority of WiFi solutions rely on omnidirectional antennas. These are antennas that transmit their signal equally in a 360-degree fashion. These are important facts to consider because even if the Starbucks is completely void of customers when you show up and log in, a hacker could easily sit in the parking lot at the back of the building and eavesdrop on the radio waves being transmitted between your laptop and the AP. Yes, you should be scared if you see someone in a car pointing a Pringles can at Starbucks with a laptop in the passenger seat. In security parlance, this hacker is known as a man in the middle (MITM).
Open APs like those at Starbucks and airports should be self-explanatory- there is no security! Yet, every time I visit the airport I’m shocked at the number of people checking their bank accounts, looking at their insurance company explanation of benefits, etc. There is a terrible misconception here that the sites are using SSL, so no one else can see the transactions taking place. This is simply wrong- SSL over an open WiFi is completely unsecured!
How SSL Works and Doesn’t
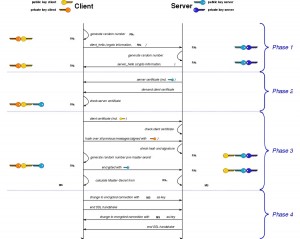 The reason is a direct result of the way all SSL works :
The reason is a direct result of the way all SSL works :
- Browser checks the certificate, attempting to match the site with the details embedded within the certificate.
- Browser and the web site server negotiate a level and type of encryption that they both understand.
- Browser and web site server then send each other a set of unique numbers they each use in a mathematically formula to algorithmically extract an encryption key that they will both use.
- Browser and web site server start exchanging symmetrically encrypted data using the key that both algorithmically extracted.
Remember that MITM sitting out in the parking lot? Tools like dsniff give hackers enough power to drill through even SSL. Short of implementing a full VPN solution, not even Gmail over SSL is considered safe, though it is more susceptible to SlideJacking than MITM. For those looking for a more thorough description of SSL MITM attacks, head over to Sans.org and check out their article on MITM attacks.
The most important lesson here is the following realization: all data transmitted between a client and an open AP is unencrypted, rendering that lock in the browser ineffective.
AP Security Options
Wired Equivalent Privacy (WEP) is another WiFi AP security option. In the spirit of time, WEP is a dead security protocol. I’ve heard security personnel bluntly say that an open AP is more secure than a WEP protected AP. Their rationale is simple–if you believe you are on an unsecured connection, you’ll be more security conscious. WEP merely creates a false sense of security. WiFi Protected Access (WPA) was intended to replace WEP. Suffice to say, WPA is considered a dead security protocol by the security industry as well, highly susceptible to attack.
 WiFi Protected Access 2 (WPA2) has replaced WPA. For our purposes, WPA2 defines Personal and Enterprise variants. The Personal variant relies on a pre-shared key. WPA2-Personal is also known by the moniker WPA-PSK, for pre-shared key. When Bob comes over to visit Alice at her home, Bob asks if he can get on the Internet. Alice informs Bob that the password is secr3tf1sh!, thus sharing the key with Bob. Hacker tools like Aircrack-ng can usually break most passwords in seconds, or worst-case, minutes. The more complex the password is, the more packets that must be collected by the tool, the more time it will take–but the password will eventually be cracked. This is a brute force attack, but placed into perspective, the Aircrack-ng suite fully works on the network card of a Nokia N900 phone. The lessons here include the fact that pre-shared key encryption is only as strong as the key, and even today’s smart phones have enough CPU power to crack the passwords in an acceptable amount of time.
WiFi Protected Access 2 (WPA2) has replaced WPA. For our purposes, WPA2 defines Personal and Enterprise variants. The Personal variant relies on a pre-shared key. WPA2-Personal is also known by the moniker WPA-PSK, for pre-shared key. When Bob comes over to visit Alice at her home, Bob asks if he can get on the Internet. Alice informs Bob that the password is secr3tf1sh!, thus sharing the key with Bob. Hacker tools like Aircrack-ng can usually break most passwords in seconds, or worst-case, minutes. The more complex the password is, the more packets that must be collected by the tool, the more time it will take–but the password will eventually be cracked. This is a brute force attack, but placed into perspective, the Aircrack-ng suite fully works on the network card of a Nokia N900 phone. The lessons here include the fact that pre-shared key encryption is only as strong as the key, and even today’s smart phones have enough CPU power to crack the passwords in an acceptable amount of time.
The astute reader may be asking, “but what if the hacker shows up after I already logged into the AP with the PSK?” Well, the IEEE solved that problem for the hacker. Per the various applicable 802.11 specifications, a client must oblige and disconnect whenever it receives a de-authorization packet from the AP. The following command from a BackTrack Linux distro demonstrates how easy it is for a hacker to send this command using aireplay-ng, a tool used to inject frames:
aireplay-ng —deauth 5 —a $AP —c $CL ath0
The $AP is the MAC address of the AP, and the $CL is the MAC address of the client. Since the client only knows it received a packet over the air and cannot verify that the packet didn’t come from the closet near the bathroom, instead coming from the hacker in the parking lot–the client nods and de-authenticates with the AP. Since the operating system has cached the PSK, the next packet that needs to be sent triggers an automatic re-authentication with the AP, without bothering the user, and, voila!, the hacker captured the authentication exchange even though he showed up late to the party.
WPA2-Enterprise for all intents and purposes relies on certified security protocol plugins, allowing WPA2-Enterprise to evolve over time without changing the overall mechanics. Over a half-dozen certified security protocol plugins exist, and each have their own weakness. Similar to WPA2-PSK, tools exist to attack the various protocol plugins. Unfortunately for WPA2-Enterprise, the MITM can capture the unencrypted packets between the AP and the client that discloses which plugin is going to be used. Once that information is known, it becomes an exercise in launching the right software to attack the plugin that is in use. The asleap tool is but one example of such software.
Open Is Unsafe
WEP and WPA are dead. WPA-PSK is about as safe as unprotected sex with random people. WPA-Enterprise, the most advanced, complex, and expensive of all the WiFi security solutions, is susceptible to attack too. What about MAC filtering? Serial numbers are unique and controlled by the manufacturers, so using either MAC filtering alone or in combination with any of these other security protocols must be safe, right?
 Wrong. Using Linux as an example, since it is the most dominate platform for penetration testing and hackers alike, hackers have the ability to expressly override the MAC address on a network card in three easy steps:
Wrong. Using Linux as an example, since it is the most dominate platform for penetration testing and hackers alike, hackers have the ability to expressly override the MAC address on a network card in three easy steps:
- ifconfig ath0 down
- ifconfig ath0 hw ether 00:11:22:33:44:55
- ifconfig ath0 up
Step 1 turns off the WiFi network card. Step 2 assigns a new, arbitrary hardware Ethernet address to the WiFi network card. Step 3 turns the network card back on, and it now uses the arbitrary MAC address specified by the hacker. In fact, this is a requisite step taken by a hacker; this is how the hacker can generate arbitrary TCP/IP packets that appear to originate from the AP when in reality he is typing them up on the fly in the parking lot.
So What Should I Do?
Let’s bring it home. The most likely way you are leaking data when using WiFi comes from the fact that you’re using WiFi. Sounds hopeless, right? Well, for now the situation is indeed grim, and you are highly likely to be pwned very quickly, hacker parlance for being dominated by a god-like computer force. If WiFi isn’t secure enough for classified military data, it sure as hell isn’t secure enough for anyone to be conducting financial transactions. The real question is: is anyone out there listening in as a MITM? Until either a new WiFi security protocol emerges, or there is a way to detect MITM attacks, we have to assume that someone is listening.
For things like email, IM, and general web surfing like hitting the ITS site on a daily basis, every form of WiFi is more than adequate. For stopping your average neighbor from stealing your Internet connection for their porn addiction, WPA-PSK is more than adequate. For conducting financial transactions, all you can do is hope for the best if you can’t find a wired connection.
Additional Recommendations
At home if you have setup an AP, stop broadcasting your SSID. This creates a first level of security that will defeat nosy neighbors. Second, stop using WEP or WPA and implement at least WPA-PSK. If your AP is too old to support WPA-PSK, then throw it out and spend $75 to buy a new one that does–the $25 ones are $25 for a reason, typically offering WEP and WPA only. Good brands include Netgear and D-Link. Unless you have a zillion friends and dozens of net-enabled home devices, turn on MAC filtering. Manufacturers make it relatively easy to find such information- even my recently upgraded net-enabled TV let me find the MAC address inside of 30 seconds of digging through the menu system. Finally, if at all possible, maintain a wired network at home for your sensitive web surfing.
What is described here is security in depth, the best you’re going to get with today’s WiFi standards, making it at least slightly more challenging for the hacker. First, they’d have to discover your SSID. Then, they’d have to successfully capture a fair number of packets from a registered MAC address to brute force the PSK. Finally, even if they got through these layers (again, relatively easily for the experienced hacker), they wouldn’t see bank transactions floating through the air if these were restricted to wired connections.
This week’s article only focused on the MITM WiFi attack vectors in the context of intercepting packets being transmitted over the air. I would be remiss if I didn’t point out that once the hacker breaches the security of the AP, they are in a position to begin an attack on the network and all of the attached clients. Tools like nmap can be run to map out the entire network segment and report on open ports, known vulnerabilities, etc. Anyone running un-patched client software is highly susceptible to exploitation, thus creating even more problems as the hacker decides to play evil tricks on you, like erase your entire set of un-backed up family photos just for grins.
If this week’s article scared the bejesus out of you, then you’ll want to stay tuned for next week’s topic. We’ll be talking about how your Droid cell phone is getting off right now calling 900 numbers, without your knowledge or permission, as a result of a rootkit you didn’t know you downloaded yesterday–making someone with a bank account in the Bahamas really rich.
Main image photo credit: BBC News











Discussion