Inside Red Team Operations, Part 2: Analyzing Recon Data and The Dry Run
Inside Red Team Operations, Part 2: Analyzing Recon Data and The Dry Run
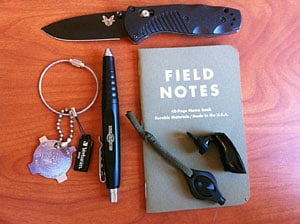
- Inside Red Team Operations, Part 1: Planning, Recon and Equipment
- Inside Red Team Operations, Part 2: Analyzing Recon Data and The Dry Run
- Inside Red Team Operations, Part 3: Execute, Execute, Execute!
 Today we’ll be looking at the 2nd part of our Inside Red Team Operations series, which takes us through the process of planning, preparing and executing a security vulnerability assessment and penetration test; bad-guys style.
Today we’ll be looking at the 2nd part of our Inside Red Team Operations series, which takes us through the process of planning, preparing and executing a security vulnerability assessment and penetration test; bad-guys style.
In Part 1, we looked at some of the elements and techniques for planning the operation and the recon. In this part, we’ll see how the information gathered during the 1st phase can be used to plan the operation.
Sorting Through Recon Data
Through OSINT, social engineering, phone probes and physical recon, we collected a large amount of data about our target. Some of that information is useless and some is the key to the success of the operation. Going through the information is tedious work but it can be rewarding.
Focusing on People
The first focus is on people. We collected email addresses and information about their employees. This should give us a clear picture of the who’s who in the company, or at least one or two names we can use to mount a social engineering attack. I usually focus on the people that hold mid-level positions. They tend to be well informed about what’s going on and are usually very helpful on the phone or over emails. That willingness to help usually comes from a person wanting to climb into a better position and want that extra “you see? I am very helpful and people rely on me” message to be spread.
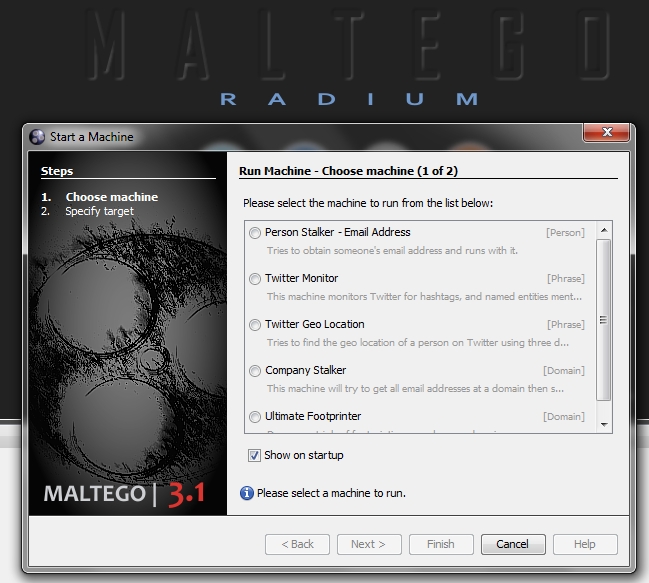
Once we have a name, we can search all the information we have about that person. If needed we can perform a deeper recon on him/her. There are several websites that provide information about a particular person, however social media sites like Facebook, Twitter and especially LinkedIn provide all the information we may need.
Products and Technologies
The second thing we focus on is products and technologies. A huge part of a successful social engineering attack is having your facts straight. If the target is a company manufacturing/developing products, they usually have them listed on their Website. Focus on those and try to get the product owners, managers, developers, spokesmen, etc.
If the target is an organization (either private or government) then the focus should be on the service these organizations provide and the points of contact.
Infrastructure
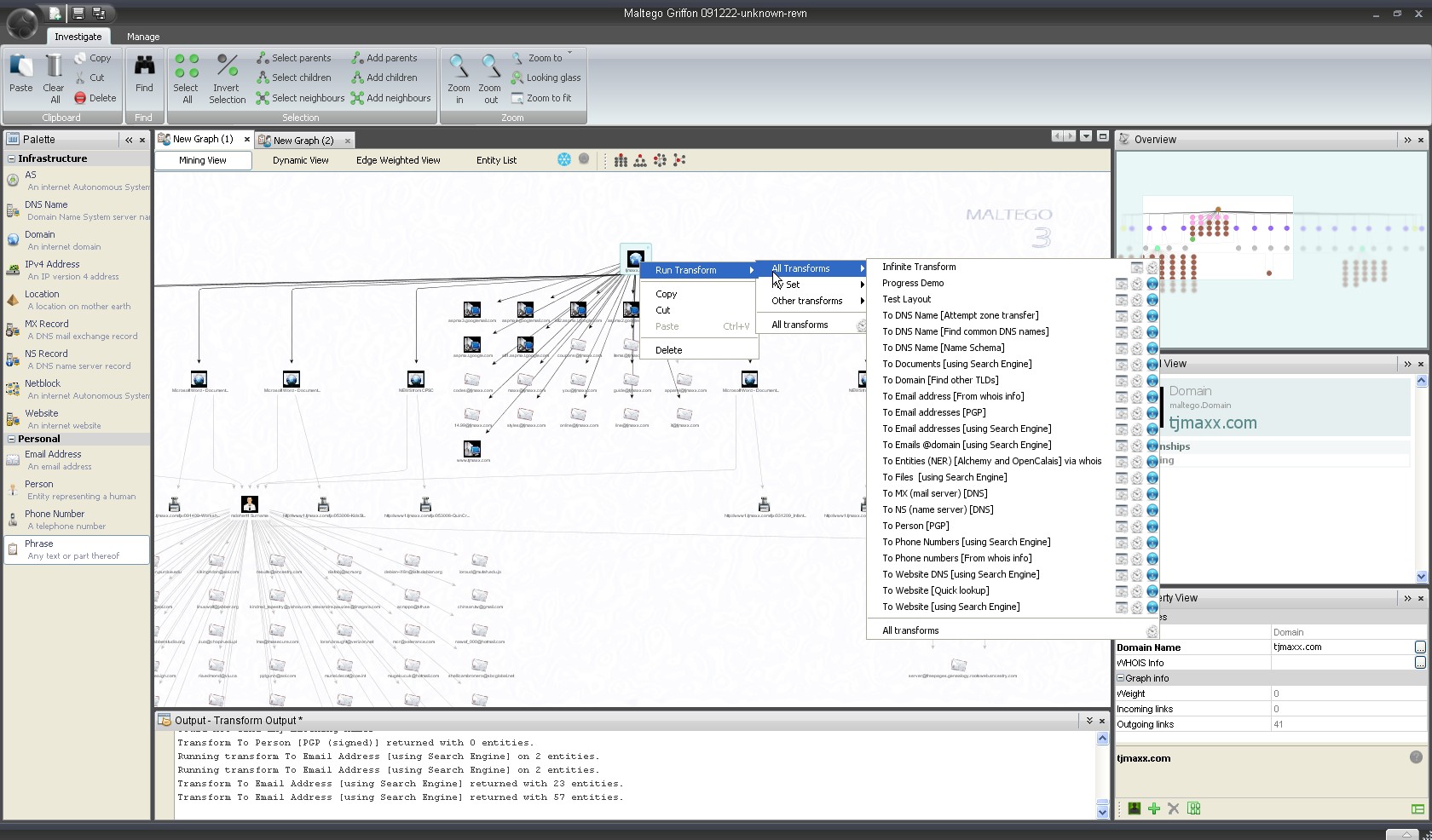
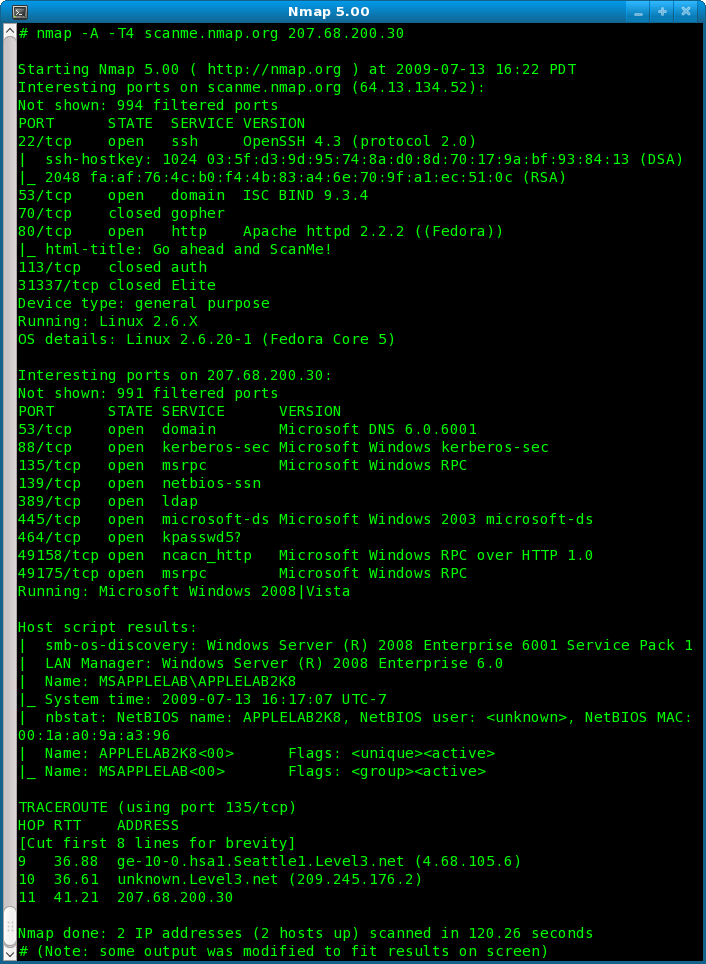
Finally we focus on the technology, or more specifically what powers their networks, web servers and their IT infrastructure. This includes informational scans for things such specific product names and versions, problems with them as reported by their own IT people. Backend and frontend technologies such as any database, CRM or other data management, web services technologies and code.
This information will allow us to start planning any possible penetration via the exploitation of a technical vulnerability. For example, if I know their main web page is hosted on a Windows 2003 Service Pack X, with IIS X.x and MS SQL Database X, then I’ll be able to pinpoint a possible vulnerability that might not be patched in this system and either find an exploit for it or write my own.
In our project, we want to be able to penetrate the company’s network and if that fails, penetrate the company’s premises. Sorting through the data, we found that the VP of marketing’s email address is listed as a point of contact on a bird watcher’s forum.
How is this relevant? Well, we now have “something in common with the VP.” We’re going to become not only an expert bird watcher, but “all the sudden” there is a new bird watching expo being planned in a few months. Since this VP is such a successful business person, we’d like him to be one of the keynote speakers at this expo. How’s that?

Preparing The Bait
The first thing we need to do is get our facts straight. We don’t need to learn everything there is to bird watching, but take 24 hours to read about it, familiarize yourself with the jargon, the hot spots in the country and local area. You want to sound credible.
Second, buy a domain that reflects the “bird watching expo” that is coming up soon. For example, birdwatchexpovegas.com, or something similar. This will be our bait. We’ll use this Website to try and exploit the vulnerabilities we may find in their system, or if this fails, as a supporting site for our cover story.
It would be a good thing at this point to try to figure out what kind of laptops/workstations the employees use. Knowing what OS (version, patch version, etc.) will help us narrow the possible vulnerabilities we can exploit.
One way to do this is by calling and using social engineering to get any number of employees to disclose that information. Another is to directly approach our target with an email.
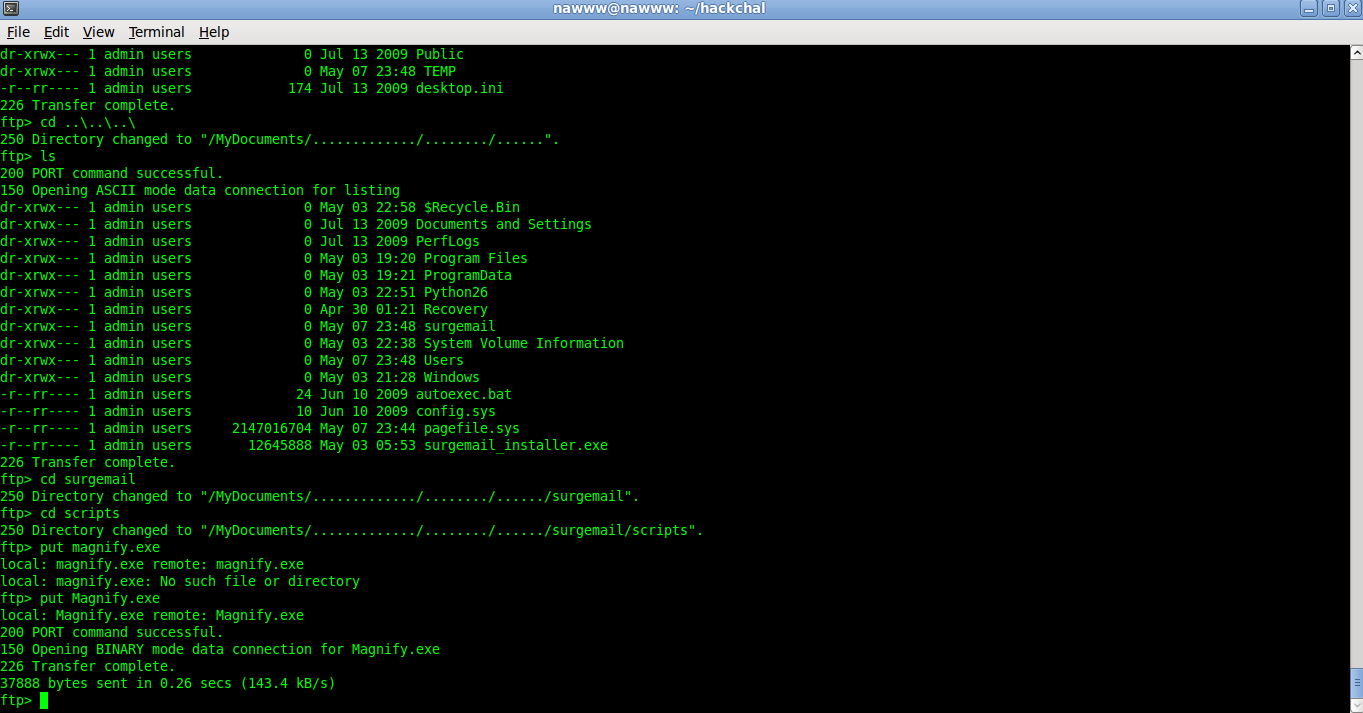
His company email is the point of contact for the bird watchers forums, so he is expecting to see bird watching related stuff on this inbox. Using the Website we just created we add a little piece of code to the page that can extract some of the information we need. We then can craft a very convincing email directing the target to our site.
If this works, then we’ll have a file sitting on our server with enough information about his browser and system for us to be able to pinpoint a vulnerability that can be exploited. On top of this, it’s often safe to assume that large corporations and organizations don’t have the latest patches, so we can use 0day exploits as well and see if they’ll work.
A good thing to have at this point is a good attack that can be spread via a PDF or a Word document. Those two file types have a lot of potential for hiding exploit code that can leverage Adobe Reader and Microsoft Office, two products with a LOT of vulnerabilities. Another good technology to exploit is Flash. You’d be surprised at the things you can do with Flash. We could use the PDF or Word Doc on an email and the Flash on our Website.
Dry Run
Before we can try all of this on our target we need to perform a dry run. This will be used to not only test our code (Website, exploits, etc.) and our script (the social engineering script, the cover story,) but to also polish the whole plan and have contingencies for every part of it. What if the exploit doesn’t work? What if the target is not interested in the expo? What if he is using a web browser that has been patched? What if his secretary is the one answering the phone? A lot of things wind up not working out.
We need to go through the whole attack and figure out the weak points. If you can, bring someone that isn’t involved into planning and have him/her poke holes in the plan. You’ll be surprised at the things you miss when you’re extremely focused.
Now comes the tricky part. We need to replicate the target environment as closely as we can. That’s when the initial digital recon comes into play. We performed informational scans using one of many tools. We should have enough information about their internet facing network and some of the employee’s workstations in order to prepare our own copy of those systems. Grab a good server, install a virtual machine manager and start cracking.
Do they use Linux for their mail server? Do they use Windows with IIS for their website? Do they have Firewalls? Routers? Any other security device that can be detected? It’s important to note that in most cases, an informational scan will return minimal information, so it’s necessary to go head first into gathering more. This can be done by either calling or visiting the target.
Once we have out servers and workstations ready have your team play the parts and have a person not involved in the planning play the target. Follow the flow and see where it fails.
Stay tuned for Part 3, where we’ll execute the operation and see how to react when things don’t go as planned!











Discussion