Are Smart Rifles a Vulnerability Nightmare? Don’t Panic Just Yet.
Are Smart Rifles a Vulnerability Nightmare? Don’t Panic Just Yet.

Imagine a “smart rifle” capable of being programmed to track a target at an unknown distance, determine the atmospheric conditions it’s operating under and reliably adjust itself in order to hit its target, no matter what. Now imagine a malicious hacker with the ability to co-opt control over that rifle and misdirect those precise shots.
As you can imagine, this scenario has the potential to be a dangerous nightmare for anyone down-range from such a device. Despite recent news indicating that this may be a very real possibility, the reality is less ominous; requiring a series of unlikely circumstances in order to occur.
TrackingPoint
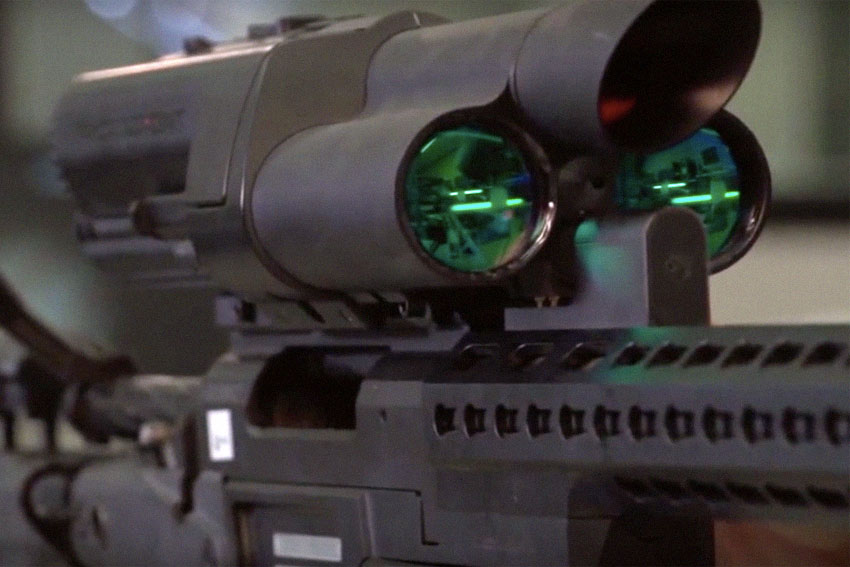
TrackingPoint is, or was, a company dedicated to producing “precision guided firearms” for hunting and potentially for military and law enforcement applications. They created an optics system with a Linux computer that was either attached to an integrated firearm that they supplied or attached to the top rail of a shooter’s own weapon.
This would allow the shooter to select and mark a target, after which the Linux computer would use the optic’s built-in laser rangefinder to determine the distance to that target. It would then calculate, based on the user-fed ballistic information for the pertinent ammunition being used, what is called a “shooting solution.”

This shooting solution would also factor in atmospheric information and adjust the video feed on the optic to provide feedback via a secondary reticle. The shooter could then move the rifle in order to merge his or her own marked target with the computer-supplied reticle, at which point the shooter could take their shot by pulling the trigger.
The basic idea behind TrackingPoint’s offering was to take precision shooting’s complicated mathematics out of the user’s head (and/or pen and paper), perform them automatically and make sure that the shooter’s first shot was a hit. The appeal of such a system should be obvious to anyone who’s ever done any long range shooting. Though predictable, the practice of precision shooting is a complicated one and has a relatively steep learning curve as opposed to closer range shooting skills.

One must learn how to accurately determine the distance to a target, factor in the known properties of the ammunition, determine the speed and direction of wind between the shooter and target and then calculate the adjustments needed to compensate. In target shooting, hitting on your first shot is less crucial than it is for hunting or sniping in Military and Law Enforcement practice.
In hunting, missing your first shot can alert prey to the fact that they’re being shot at and they’ll likely react by leaving the area rapidly, making subsequent shots increasingly difficult. In Law Enforcement or Military situations, missing that first shot can mean not only alerting your target, but also potentially hitting someone or something you didn’t intend to, such as an innocent hostage.
History

TrackPoint initially offered the computerized scope, but eventually discontinued that option in favor of only fully integrated scopes with the firearm attached. It’s hard to say just how many were sold in the civilian market, as the price of these systems was steep, running from $7,495 and up to $49,995 depending on the rifle system. In contrast, a bolt-action Remington 700P costs somewhere in the $2000 range; adding a top-of-the-line traditional optical scope may cost another $2000-$3000, bringing the total for a standard Police rifle system to about $5000. This is less than half of the comparable entry-level TrackingPoint system.
Given that the use of the TrackingPoint system still requires a trained shooter, it was (and is) still more cost-effective to purchase a traditional system and send the shooter through traditional long-range training, wherein they would be taught all of the skills that the computer would be performing on the TrackingPoint equipment. Though TrackingPoint has provided the rifles for testing to the Department of Defense, they are unable to say whether the rifles are in use by DOD forces or not.

Instead they prefer to point out that DOD informed them their rifles would be considered ITAR-affected products and therefore would not be allowed to be exported without the permission of the State Department. Marketing aside, classification as a “defense article” by ITAR does not determine actual in-field military use of an item, it simply means that the item does have a potential defense use and is therefore restricted by ITAR.
In May of 2015, TrackingPoint announced $20 million in sales, then subsequently laid off a sizeable portion of their work force and stopped accepting new orders. Speculation and rumors are plentiful as to the actual reasons for the reduction of employees, but these are outside the point of this article. The only official statement from TrackingPoint was a notice on their website stating, “Due to financial difficulty TrackingPoint will no longer be accepting orders.”
The Hack
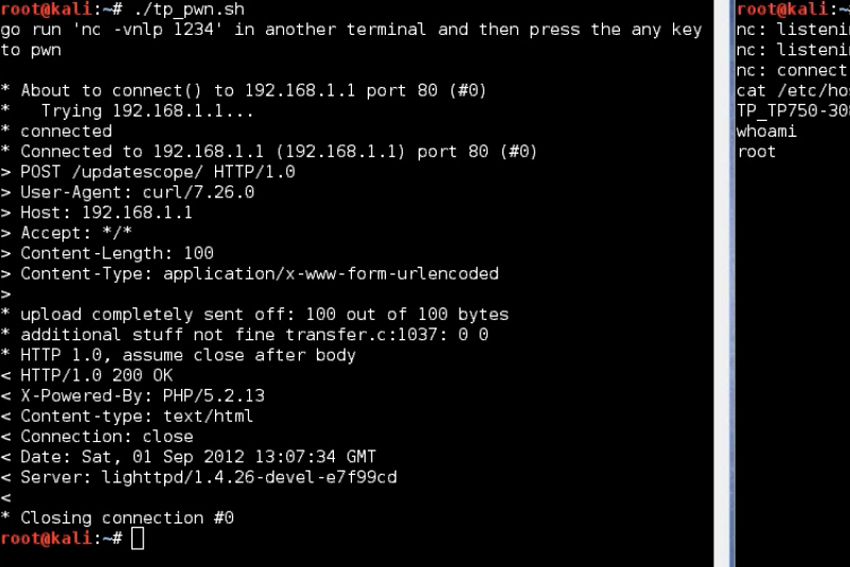
More recently, TrackingPoint made national news when two security researchers on the East Coast of the US claimed they had hacked the TrackingPoint system, allowing for remote control and manipulation of the rifle by someone other than the shooter over Wi-Fi. Runa Sandvik and Michael Auger made their announcement and gave a presentation at the Black Hat conference in Las Vegas. They described the process they used to achieve the hack and the pitfalls they encountered along the way.
As described in their presentation, the process of hacking the TrackingPoint rifle took a year to complete and was complicated. In the end, they were able to replace the TrackingPoint Linux operating system with a modified version of the OS, which enabled a remote user with root privileges to access it. If within Wi-Fi range of the rifle, they could basically feed the ballistics calculation process with bogus data, thus making the shots the shooter took miss the intended target. They were also able to entirely disable shooting the rifle by controlling the solenoids connected to the trigger of the rifle.
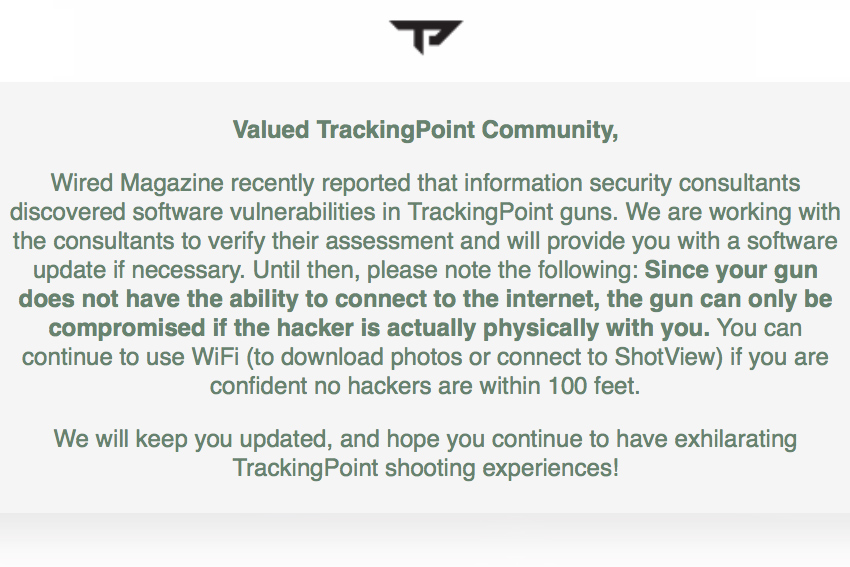
While this garnered a fair amount of sensationalist press, the real effects were overplayed. In order to take control of any given TrackingPoint rifle, Wi-Fi first had to be enabled by someone with physical access to the rifle; on TrackingPoint rifles Wi-Fi is turned off by default. After that, the operating system had to be “upgraded” to the corrupted version of the OS and only then could they exert their remote control exploits. InRange TV attended the presentation and did a fairly thorough breakdown in their video piece of what was actually required to perform the exploit.
The takeaway from all of this information provided is that the “hack” is, by default, not possible and requires close physical proximity and physical access to perform. If the rifle owner could be persuaded to turn Wi-Fi on, distracted while the operating system is replaced and if the attacker remained in physical Wi-Fi distance, they could gain access to the rifle’s operating system. They could then cause the shooter to either miss the target, or prevent the shooter from firing.
Then again, if an attacker is within Wi-Fi range of the rifle and had initial physical hands-on access to the rifle, they could disable it by doing something as simple as taking a hammer to the scope or barrel or even throwing a large object at the shooter. Even loudly yelling near the shooter when the shooter was preparing to take their shot would possibly provide the same end result of a missed shot.
While the story of a “hacked smart rifle” may gather loads of alarmist Internet traffic, the reality is a little more subdued. Not only does the described “hack” require the noticeable presence of an attacker and distraction or diversion of the victim for a substantial length of time, there simply aren’t that many of the target devices in the wild to merit the level of fear, uncertainty and doubt the media is trying to manufacture.
If TrackingPoint ever drops prices to the point that these “smart rifles” become a lot more ubiquitous, there might be more cause for alarm. Even then, it’s highly likely they will have addressed the current vulnerability, rendering it moot by that point. Given their current insecure financial status and shaky future though, it may be a long while before shooters need to check a 100 foot radius for “hackers” before sending lead downrange.
Editor-in-Chief’s Note: Matthew Sharp is a Plank Owner and Life Member at ITS and goes by the username “viator.” He lives in The People’s Republic of Northern California and enjoys long range shooting, carrying heavy objects great distances and fuzzy little puppies.











Discussion